Local Admin Rights, Managed.
Eliminate Local Admin Rights.
-
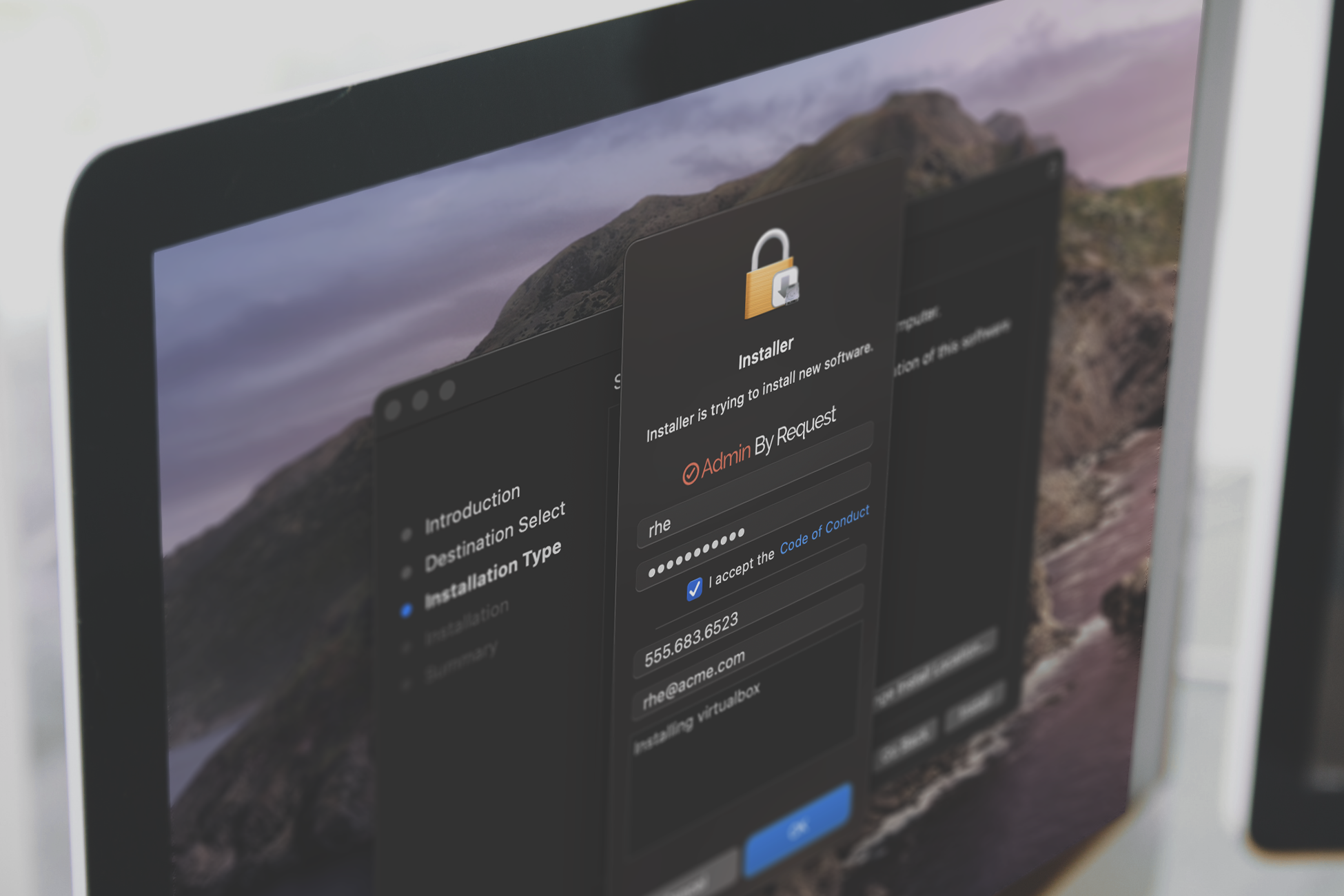
Your users will never know they lost them
-
No one in IT has to install software or create whitelists
-
Let us show you your future - without local admin rights.

Full control at your fingertips.
Why Choose Us?
A high-level look at the what, why, and how
App Elevation
Elevate applications without elevating the user
Break Glass / LAPS
Provision temporary local admin accounts
Malware Detection
Multi-scanning with over 35 engines
Endpoint MFA/SSO
Enforce business rules with MFA and SSO prior to elevation
AI Approval
Allow our AI engine to auto-approve requests for elevation
Machine Learning
Allow auto-approvals after a set number of manual approvals
GDPR Compliance
Ensuring all sensitive data is protected
Our Customers
Trusted by Global Leaders

''We use Admin By Request to manage local admin rights at Atos on more than 100.000 endpoints in 60 countries. We would definitely recommend Admin By Request to any organization looking to solve the local admin rights problem.''


Admin By Request Milestones
Take control of your local admin accounts
Revoke without the revolt
Poeple we've helped
Here's what they're saying
Numbers at a Glance
The Problem
Employee workstations are one of the most vulnerable parts of your company’s IT system.
Lack of Security
Your employees' workstations can be easily compromised if a user with Local Admin Rights runs an executable that contains malware.
Compromised Network
The Network security of your company can be compromised by an attacker to steal data, financials, and IP if just one compromised user is operating with unrestricted local admin rights.
Disrupted Productivity
Removing Local Admin Rights from managed endpoints mitigates critical vulnerabilities but prevents users from running every-day, trusted tasks that require privilege elevation.
Impacted Performance
The lack of Just-In-Time Privileged Access Management (PAM) can lead to a decline in staff productivity, impacting on the company’s overall performance.
The Solution

Gain Admin Rights Compliance
With rapid provisioning of Just-In-Time privilege elevation across your entire workforce. On-board and manage workstations and servers via a user-friendly portal.

Monitor and Audit Behavior
To reveal risky users and assets through thread and behavioral analytics to identify malicious software and prevent data breaches and malware attacks.

Enhance User Productivity
By elevating applications - not users. Delegate privileges based on the user or groups to save time and monetary resources.
See it in action
Core Features
Ways to Elevate
Run as Admin
Elevate a single application.
Break Glass / LAPS
Provision temporary / emergency local admin accounts.
Machine Learning
Create Pre-Approved lists as employees use the software.
Admin Session
Gain admin rights for a period of time.
Pre Approvals
Decide which programs are safe and allow elevations for them ahead of time.
AI Approvals
Let our Artificial Intelligence engine decide what's safe for auto-approval.

All Key Features
Available on Mobile
Dashboard
Provides a summary of your subscription, usage, recent activity, clients, and recently installed software.
Auditlog
Records details from all elevated sessions, including the user who initiated, reason for elevation, programs executed, and software installed.
Requests
Displays all requests for elevated privileges that are pending approval, with the option to approve or deny these requests from your mobile device.
Inventory
Lists the hardware and software details for all devices that have Admin By Request deployed, including disk space, location, and software versions.
Improve your Workflow
Integrate
Admin By Request
With your favourite software tools.
Get Protected
Sign up for our Free Plan
No strings attached.
Problem | Solution | Implementation
Case Studies
Stay Up To Date
Latest Blogs
Combating Common Ransomware Tactics
In the unrelenting battle of the good guys versus cybercriminals, ransomware perpetrators have come out swinging in 2021. This blog investigates the common behaviors of the latest attackers on...
Don’t Cut Corners While Running LAPS
Microsoft LAPS was released in 2015 with the main purpose of making it more difficult for hackers to spread accross IT networks. This Infosecurity Magazine blog explains how MS...
ISO 27001: Certified
You've seen it before, but what does it actually entail? In a nutshell: security, sustainability, and continually improved products and services. Admin By Request is now ISO certified, and...
Are You Responsible for Losing the Mothership?
It doesn't matter how many high-tech defenses and security systems you have protecting your network – they can all be thwarted if you let hackers slip onto the Mothership...
Cyber Privilege Access Management in No Time
How Admin By Request enables you to comply with UK Cyber Essentials privilege management requirements.
Privileged Access Management Just Got Personal.
The terms ‘use case’ or ‘usage scenario’ are cold and soulless words and not a good representation of the type of work we do here. Introducing ‘Usage Persona’: a...